Hey there,
I hope you had a great weekend!
In this week's issue:
Spending priorities
Thoma Bravo cannot be stopped
Funding continued to drop in Q3 2022
Thoma Bravo’s bloodlust seemingly knows no bounds. Last week the identity and access management (IAM) company, ForgeRock, was the latest target (see below) for Thoma Bravo who is on a streak of IAM acquisitions. Thoma Bravo has already acquired SailPoint in April 2022 and Ping Identity in August 2022.
The ceiling is the roof for @thomabravo pic.twitter.com/p8Un9fsUnB— Mike Privette (@mikepsecuritee) August 17, 2022
Thoma Bravo has found a great wedge to make a big bet on - the battle of who controls identity in the enterprise.
With Thoma Bravo locking in on the IAM space by acquiring competitors who capabilities compliment and overlap each others, they will have secured themselves a large return on security investment (see what I did there?).
From a CISO's point of view, IAM capabilities make up a huge percentage (> 50%+) of the annual security budget for most enterprise security programs. Compliance frameworks, regulators, and auditors all care about access as a core component of reducing risk and it's a place that most organizations struggle with when it comes to tech debt. As a result, IAM gets a lot of attention. And cash.
Expect to see an increase in new identity-based governance and threat detection platforms in 2023 to attempt to solve old problems in novel ways.
Cybersecurity funding continued its downward trend in Q3 2022. Both overall volume of transactions and total amount of money raised took a hit.
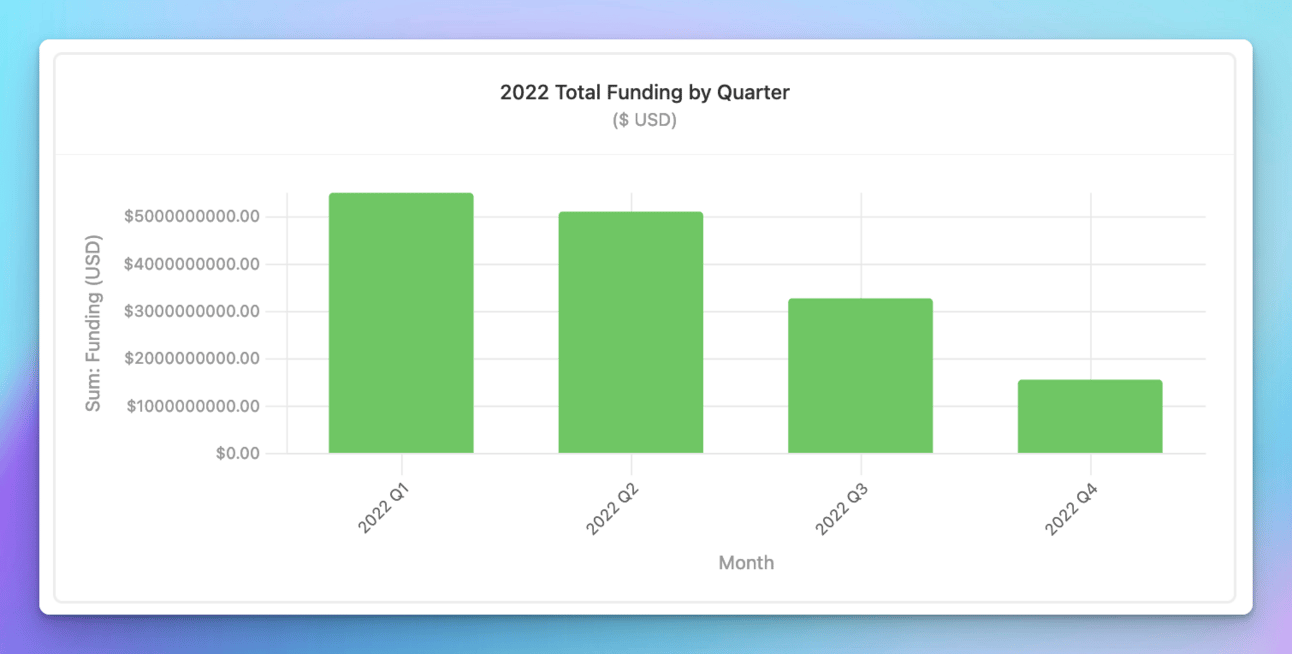
Source: from a live dashboard I made
What is interesting, however, is that while the total funding volume is down, the average funding round check size is still on par with 2021 to the tune of $29.1M in 2022 compared to $29.8M in 2021.
Q4 2021 saw a rebound in transaction volume and money, and based on how October has started, this trend appears to be happening again in 2022.
Onward to this week's issue.
🚨
I'm now opening newsletter sponsorships for the first half of 2023! If you would like to get your company in front of some of the most influential eyes in the cybersecurity and investing industries, reach out to learn more.
Subscribe to Security, Funded
Know what and who is moving the cybersecurity.
🗣️ SPONSOR
🗣️
Avoiding Career Lateral MovementIn less than one episode of Ozarks, hear my own career advancement story and get the actionable steps, checklists, and action prompts I've used to advance my own career.I’ve done a lot of guessing, checking, and iterating (i.e., changed jobs a ton) and I’ll share what has worked and continues to work for me.Let's get this bread together, family. 🥖
📊 Industry News
💰 Funding Summary
18 companies raised $512.7M across 15 unique product categories
6 companies were acquired or had a merger event across 5 unique product categories for $6.9B
🧩 Funding by Product Category
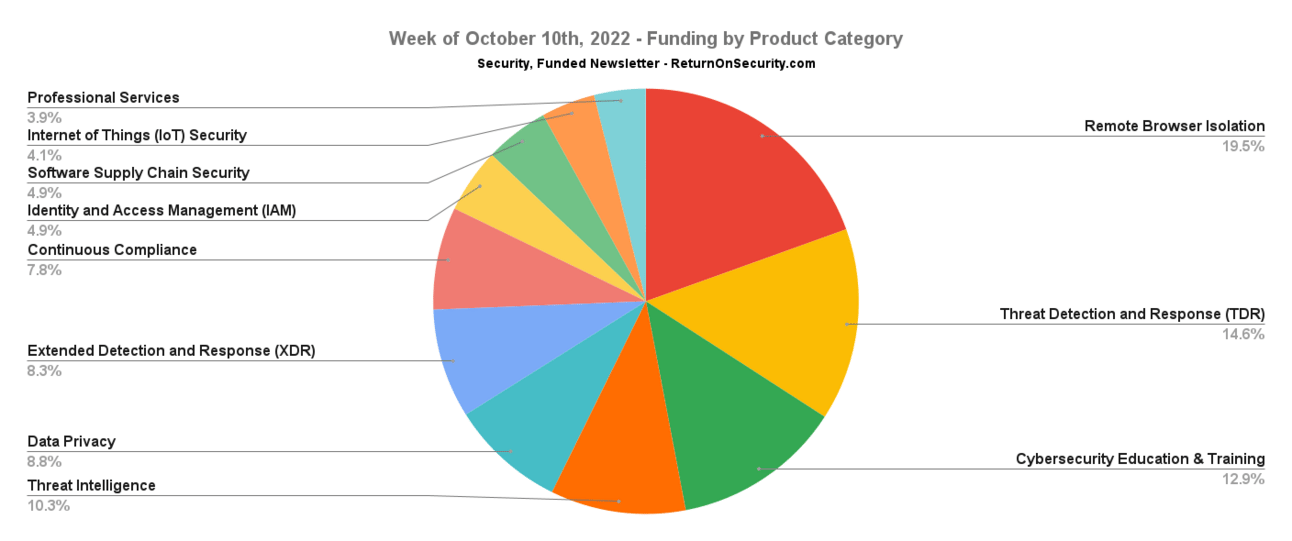
$100.0M for Remote Browser Isolation
$75.0M for Threat Detection and Response (TDR)
$66.0M for Cybersecurity Education & Training
$52.7M for Threat Intelligence
$45.0M for Data Privacy
$42.6M for Extended Detection and Response (XDR)
$40.0M for Continuous Compliance
$25.2M for Identity and Access Management (IAM)
$25.0M for Software Supply Chain Security
$21.0M for Internet of Things (IoT) Security
$20.0M for Professional Services
$180.0K for Managed Services Provider (MSP)
An undisclosed amount for Threat & Vulnerability Management (TVM)
An undisclosed amount for Secure Remote Access
An undisclosed amount for Data Protection
🏢 Funding By Company
Immersive Labs, a cybersecurity education and training simulation platform, raised a $66.0M Venture Round from Ten Eleven Ventures. (more)
DataGrail, a data privacy management platform, raised a $45.0M Series C from Third Point Ventures. (more)
Stairwell, a threat hunting detection and response platform, raised a $45.0M Series B from Section 32. (more)
Citalid Cybersecurity, a cyber threat intelligence platform, raised a $42.7M Series A from Jolt Capital.
TEHTRIS, an extended detection and response (XDR) platform, raised a $42.6M Series B from Jolt Capital. (more)
Vanta, a continuous compliance and security platform, raised a $40.0M Series B from CrowdStrike Falcon Fund. (more)
Field Effect, a threat detection and response platform, raised a $30.0M Series A from Edison Partners. (more)
Endor Labs, a software supply chain security platform, raised a $25.0M Seed from Dell Technologies Capital, Lightspeed Venture Partners, and Sierra Ventures. (more)
IronVest, a password manager application, raised a $23.0M Seed from Accomplice. (more)
Securithings, an Internet of Things (IoT) security platform, raised a $21.0M Series B from U.S. Venture Partners. (more)
Dream Security, a critical infrastructure security consulting company, raised a $20.0M Pre-Seed from an individual angel investor. (more)
Lumu, a threat intelligence platform using DNS to determine potential compromises, raised a $10.0M Debt Financing round.
Rownd, a low-code authentication-as-a-service platform, raised a $2.2M Seed round.
KubeNet, a managed services provider (MSP) focused on managed network, voice, and endpoint security, raised a $180.0K Grant from Scottish Enterprise. (more)
Cyolo, a zero trust network access (ZTNA) company, raised an undisclosed Venture Round from IBM Ventures. (more)
Intertrust, a data protection and governance platform, raised an undisclosed Corporate Round from JERA. (more)
🤝 Mergers & Acquisitions
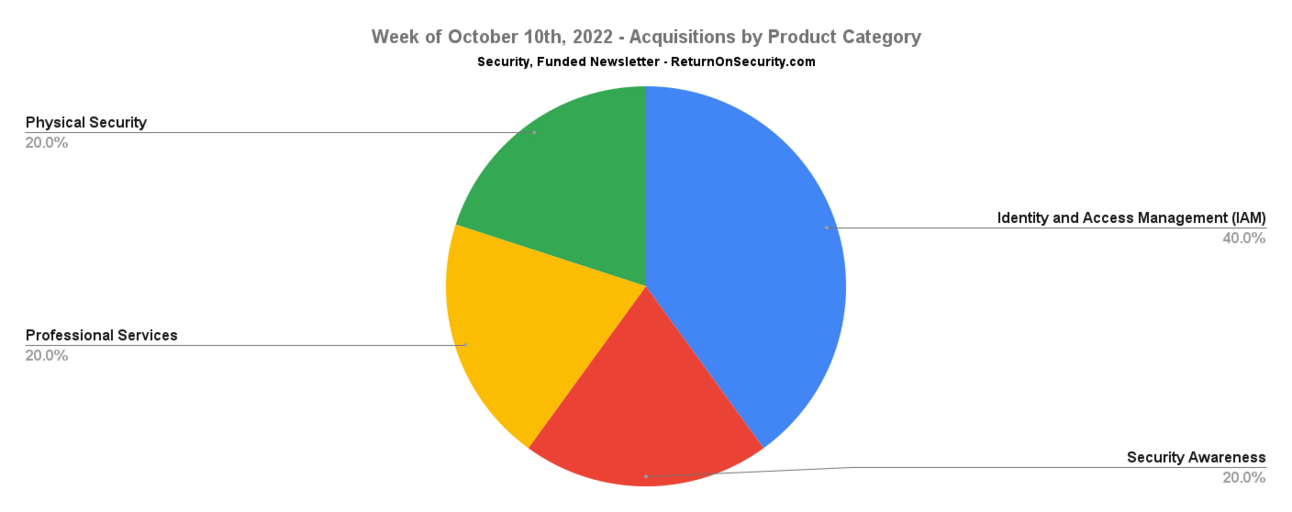
KnowBe4, a security awareness and simulated phishing training platform, was acquired by Vista Equity Partners for $4.6B. (more)
ForgeRock, an enterprise identity and access management (IAM) platform, was acquired by Thoma Bravo for $2.3B. (more)
Authlogics, a password management platform, was acquired by Intercede for an undisclosed amount. (more)
Blue Star Security, a physical security services firm, was acquired by Protos Security for an undisclosed amount. (more)
CSIS Security Group, a professional services firm focused on e-crime and fraud prevention, was acquired by Allurity for an undisclosed amount. (more)
🔐 Secure The Job
If you're looking for new opportunities (actively or passively), I've got two ways to help:
Return on Security Job Board - Browse the jobs I curate each week and apply for what matches your interests.
Return on Security Talent Collective - Apply to my talent collective to get personally matched with high-growth, high-upside opportunities.
Are you hiring? Post a role and request access to start meeting world class candidates open to new opportunities. Learn more or request access here.
📚 Great Reads
Cyber Security Career Pathways - Common career pathways within the security industry to contextualize where Cloud Security fits into the big picture.
Secure your machine learning with Semgrep - To strengthen the ML ecosystem, Semgrep analyzed the source code of many ML libraries and identified some common problematic patterns.
Securing the U.S. Electricity Grid from Cyberattacks - Reliable electricity is essential to the conveniences of modern life and vital to our nation’s economy and security. But the electricity grid is an attractive target for cyberattacks from U.S. adversaries—such as nations like China and Russia, as well as individual bad actors, such as insiders and criminals.
You can see the full list of curated posts across all issues here, and you can submit an article, post, tweet, or video here and it can show up in the newsletter!
🧪 Labs
Cybersecurity Awareness Month Tip #5:
If a big attacker is close by: Stay in a group; carry junior developers; make noise. Do not run and do not bend down to pick up code.
Act dominant and stand your ground — stare in the attacker’s eyes and show your teeth while making noise.— Kelly Shortridge (@swagitda_) October 5, 2022
👋 Thanks
Have questions, comments, or feedback about this issue? I'd love to hear from you. Reach out on Twitter or reply directly to the newsletter version of this issue.
Thanks for reading and see you again next time!
Whenever you're ready, there are a few ways I can help you:
Cheers,
Mike P