Security, Funded is a weekly deep dive into cybersecurity funding and industry news captured and analyzed by Mike Privette. This week’s issue is presented together with MineOS and Anvilogic.
Hey there,
I hope you had a great weekend, and maybe even a long one if you’re in Europe with the bank holidays! Also, happy end of Q1 to all those who celebrate. 🥳
This weekend, I was looking for some kind of aphorism or statement to help convey what it feels like the cybersecurity industry has gone through in Q1 2024, and I landed on this one:
Our life is March weather, savage and serene in one hour.
I’ll be releasing a monthly report for March soon, but this really sums up what the high-velocity funding rounds, M&A activity, and all the hype around the big public players have felt like so far. If Q1 is an indication, cyber is going to have another really interesting year.
Onward to this week's issue.
Submit a deal here: [email protected]


Table of Contents

😎 Vibe Check
What is your security program's top priority going into Q2?
Last issue’s vibe check:
Where should AI Governance, Security, and Safety sit in a company?
🟩🟩🟩🟩🟩🟩 🔐 CISO Org (17)
🟨🟨🟨⬜️⬜️⬜️ 👩🏾⚖️ Legal or Risk Org (10)
🟨🟨🟨⬜️⬜️⬜️ 👨🏻💻 CTO Org (10)
⬜️⬜️⬜️⬜️⬜️⬜️ 🔮 Other (leave a comment) (0)
37 Votes
Most people felt that AI Governance, Security, and Safety should sit in the CISO org, but it is interesting how Legal/Risk and CTO orgs are split. This is certainly not a one-size-fits-all answer, but many companies are having this exact conversation and the turf wars that go along with it.
Some of my favorite comments from last week included:
“This is tough as some lines of effort fall traditionally in Risk's lane and some is most definitely in the security realm along many lines of effort.“
“It doesn't matter if the CISO or Legal org's think they're in charge...the CTO is the org that has to do it.”
This poll doesn’t even include the US Executive Order requiring US federal agencies to designate a “Chief AI Officer.” 🫣

💰 Market Summary
14 companies raised $216.3M across 10 unique product categories in 7 countries
2 companies were acquired or had a merger event across 2 unique product categories
100% of funding went to product-based cybersecurity businesses
No notable public cyber companies had an earnings call

📸 YoY Snapshot
This is a rolling 12-week chart comparing funding and acquisitions each week in a year-over-year (YoY) view between 2023 and 2024.
We’re at week 13 and at the final week of Q1 2024 now.

With the final March investments in, this has been the first month to surpass $1.0B in total funding since October 2023.
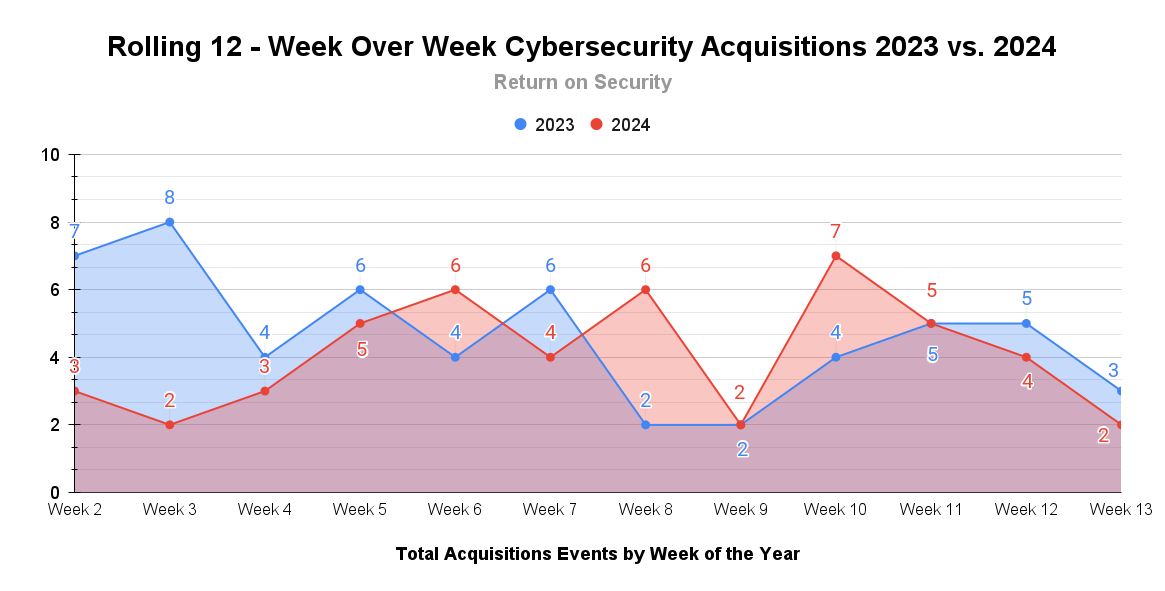
On the M&A front, while transactions have been slightly less than in Q1 2023, they have certainly been more prominent in 2024.

🤙 Earnings Reports
Here are notable earnings reports from public cybersecurity companies, be they “pure play” or hybrid companies. This section is Powered by Quartr.
See the public cyber company tracker, which shows all public cybersecurity companies worldwide, along with market data, funding raised, product categories, and more.
Earnings reports this week: No notable earnings calls.

TOGETHER WITH
Navigate the New EU AI Act
Strategic AI Governance Starts Now
With the EU AI Act reshaping the landscape, the clock is ticking for AI system compliance. See where the creators think the law falls short, Provider & Deployer requirements, and a step-by-step approach to compliance in MineOS's guide to navigating the AI Act's complexities.

🧩 Funding By Product Category
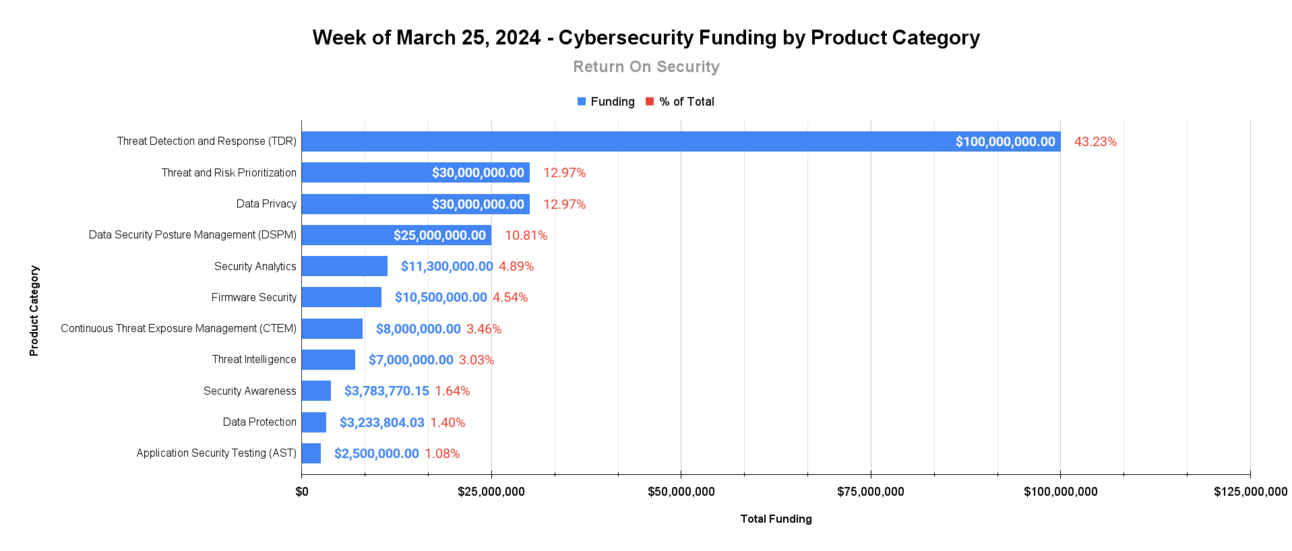
$100.0M for Threat Detection and Response (TDR) across 2 deals
$30.0M for Threat and Risk Prioritization across 1 deal
$30.0M for Data Privacy across 1 deal
$11.3M for Security Analytics across 2 deals
$10.5M for Firmware Security across 1 deal
$10.0M for Data Security Posture Management (DSPM) across 1 deals
$8.0M for Continuous Threat Exposure Management (CTEM) across 1 deal
$7.0M for Threat Intelligence across 1 deal
$3.8M for Security Awareness across 1 deal
$3.2M for Data Protection across 2 deals
$2.5M for Application Security Testing (AST) across 1 deal

🏢 Funding By Company
Skyflow, a United States-based data privacy vault platform, raised a $30.0M Series B from Khosla Ventures. (more)
Zafran Security, a United States-based threat and risk prioritization platform that uses your existing tool stack to show risks and mitigations, raised a $30.0M Venture Round from Cyberstarts and Sequoia Capital. (more)
BINARLY, a United States-based managed firmware security platform, raised a $10.5M Seed from Two Bear Capital. (more)
Bedrock Security, a United States-based data security platform using AI for data risk assessments and data posture management, raised a $10.0M Seed from Greylock. (more)
Abstract Security, a United States-based security analytics and operations platform, raised a $8.5M Seed from Crosslink Capital, Rally Ventures, and Liquid 2 Ventures. (more)
Sprocket Security, a United States-based continuous threat exposure management (CTEM) platform, raised a $8.0M Series A from Blueprint Equity. (more)
StealthMole, a Singapore-based dark web threat intelligence monitoring platform, raised a $7.0M Series A from Korea Investment Partners. (more)
Think Cyber Security, a United Kingdom-based security education and awareness platform, raised a $3.8M Seed from Fuel Ventures. (more)
DataKrypto, an Italy-based data encryption-in-use platform, raised a $3.2M Seed from Cysero and P101. (more)
Leen, a United States-based API-driven security tool and data integration platform, raised a $2.8M Pre-Seed from 11.2 Capital. (more)
SydeLabs, a United States-based automated red team testing platform for generative AI applications, raised a $2.5M Seed from RTP Global. (more)
Desilo, a South Korea-based data governance and data clean room platform, raised an undisclosed Venture Round from SV Investment Corp. (more)
Sandfly Security, a New Zealand-based threat detection and response platform for Linux systems, raised an undisclosed Seed from Alt Ventures, Gula Tech Adventures, and Sorenson Capital. (more)

🌎 Funding By Country
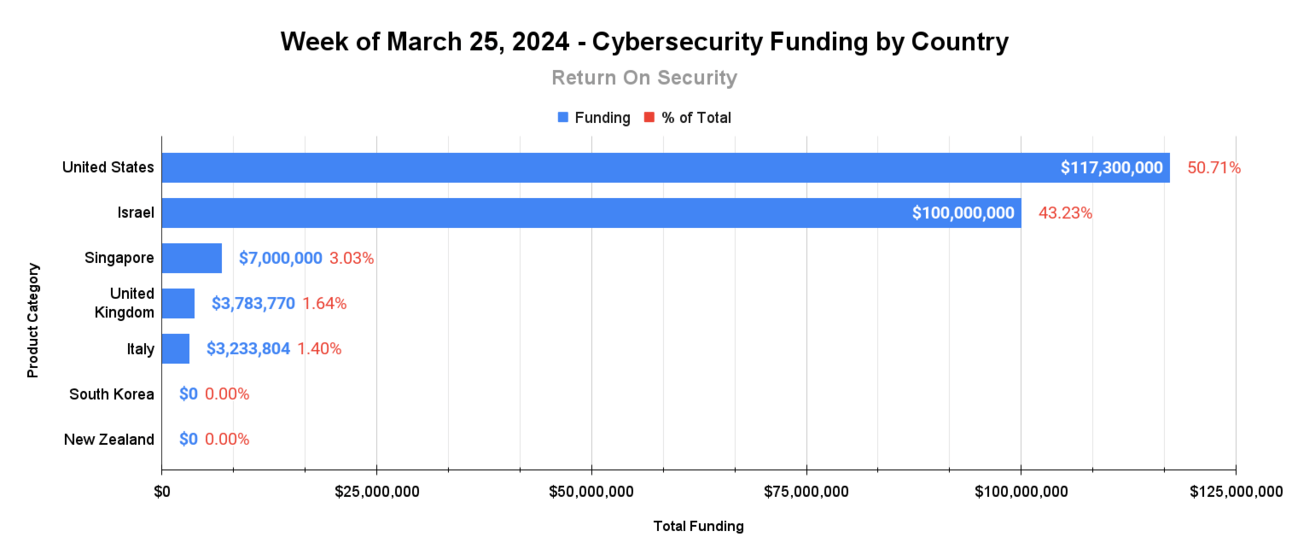
$117.3M for the United States across 9 deals
$100.0M for Israel across 1 deal
$7.0M for Singapore across 1 deal
$3.8M for the United Kingdom across 1 deal
$3.2M for Italy across 1 deal
An undisclosed amount for South Korea across 1 deal
An undisclosed amount for New Zealand across 1 deal

🤝 Mergers & Acquisitions

Digital Seattle, a United States-based managed security services provider (MSSP), was acquired by Intelligent Technical Solutions for an undisclosed amount. (more)

📚 Great Reads
The Market is Forcing Cloud Vendors to Relax Data Egress Fees - A look at how market dynamics are changing the way cloud service providers think about charging for data to leave their infrastructure. This comes at a time when next-gen SIEM and security analytics platforms are increasingly becoming their own centers of data gravity.
*The Two-Headed SIEM Monster: Endpoint security vendors have joined cloud providers in recommending their SIEM. However, the downsides to detection engineering across multiple SIEMs haven't been widely discussed. Here’s what to consider before embracing a side SIEM.
The Problem of AI Ethics and Laws About AI - Benedict Evans discusses the complexities of AI ethics and regulation, using historical examples like the UK Post Office scandal and the misuse of software to illustrate that the issue is not with technology itself but with institutional failures and misuse.
Unveiling the Art of Mastering Vulnerability Management in Cybersecurity - Metrics play a crucial role in gauging the effectiveness of a vulnerability management program, but relying solely on numbers and averages is a recipe for failure.
*A message from our sponsor.

🧪 Labs
90’s kids definitely feel this one

How was this week's newsletter?

Data Methodology and Sources
All of the data is captured point-in-time from publicly available sources.
All financial figures are converted to U.S. dollars (USD) when collected.
Company country locations are pulled from publicly available sources.
Companies are categorized using our own system at Return on Security, and we write all of the company descriptions.
Sometimes, the details about deals, like who's in, how much they're giving, or the deal stage, might get updated after we first publish the issue.
If you spot any errors, let us know, and we’ll fix them.

About Return on Security
Return on Security is all about breaking down the cybersecurity industry for you with expert analysis, hard facts, and real-life stories. The goal? To keep security pros, entrepreneurs, and investors ahead in a fast-moving field.
Feel free to borrow any data, charts, or advice you find here. Just make sure to give a shoutout to Return on Security when you do.

Thank you for reading. If you liked this summary, please share it with your friends, colleagues, and everyone interested in the cybersecurity market.

