Hey there,
I hope you had a great weekend and Shana Tova to all my Jewish friends celebrating Rosh Hashanah!
In this week's issue:
Cyber grant programs
A new kind of cyber-focused VC
The flywheel that keeps the cybersecurity industry moving
A new trend is on the horizon in the cybersecurity industry. The rise of the VC arm at cybersecurity companies. These VC arms invest in the cybersecurity ecosystem and sometimes in competitors.
SenitnelOne ($S) announced a new $100M fund via S Ventures.
CrowdStrike ($CRWD) Falcon Fund, partnered with Accel, made two investments last week alone (see below).
This type of investing is already common place in other more established industries like Financial Services.
The obvious questions - why this and why now? A simple theory - A rising tide lifts all boats.
The answer can be a bit more complex than this and it isn't always for altruistic reasons. In listening to recent earnings calls for a few publicly traded cyber companies, there's a joint go-to-market (GTM) strength in going to bat with complementary and adjacent offerings to your own.
This kind of investing can also establish the larger cyber players with plug-n-play marketplaces for other cybersecurity companies. The larger players can bring more offerings and more value to their customers and the less establishing players can get scale and market saturation much quicker than going to bat on their own. This is a similar model to what Snowflake and other have done with their marketplace.
Joint GTM strategies are paying off big time for these large companies and pushing earnings up. Way up. This strategy raises the contract value for everyone and creates deeper partnerships and recurring revenue opportunities for all players involved.
Think about this new cyber company VC as another spin on that same goal. Strategic investments create strategic partnership and strategic cash flow.
You heard it hear first folks. Watch this to continue to evolve as we move into 2023.
Speaking of evolutions, here's my take on the flywheel effect that drives the entire cybersecurity industry. Let me know what you think!
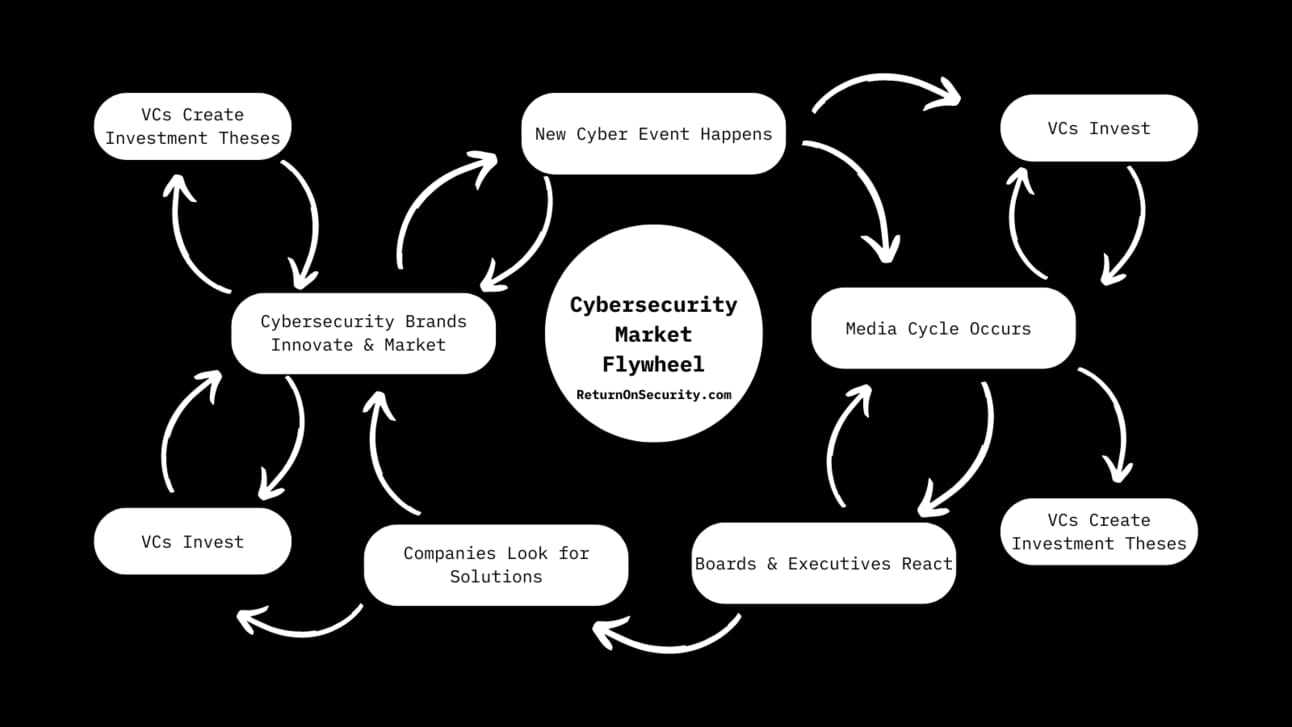
Cybersecurity Market Flywheel
Let's dive in.
Subscribe to Security, Funded
Know what and who is moving the cybersecurity.
📊 Market News
💰 Funding Summary
16 companies raised $367.8M across 14 unique product categories
5 companies were acquired or had a merger event across 5 unique product categories for $4.2B
🧩 Funding by Product Category
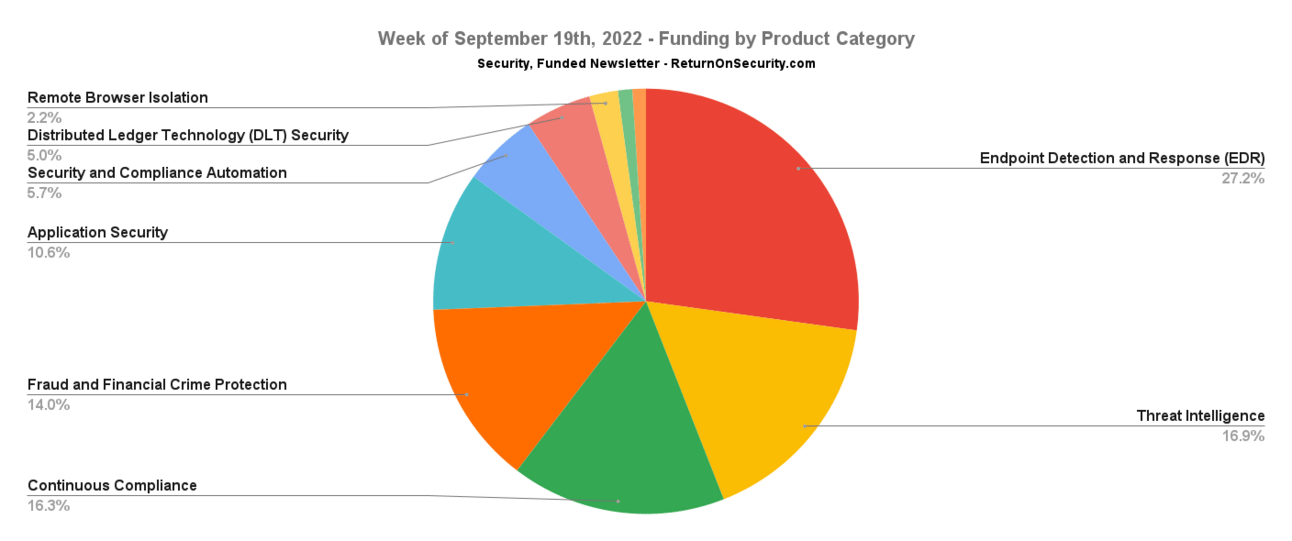
$100.0M for Endpoint Detection and Response (EDR)
$62.0M for Threat Intelligence
$60.0M for Continuous Compliance
$51.5M for Fraud and Financial Crime Protection
$39.0M for Application Security
$21.0M for Security and Compliance Automation
$18.5M for Distributed Ledger Technology (DLT) Security
$8.0M for Remote Browser Isolation
$4.0M for Privacy
$3.8M for Secure Access Service Edge (SASE)
An undisclosed amount for Software Supply Chain Security
An undisclosed amount for Internet of Things (IoT) Security
An undisclosed amount for Email Security
An undisclosed amount for API Security
🗣️ SPONSOR
🗣️
Top Five Cyber Security Threats to Digital Banking and How to Guard Against ThemBanks remain one of the biggest targets for cyberattacks – Be Prepared!The fight starts with understanding what sort of threats exist to most banks and how to stay guard against them. Let’s delve into five of these threats, including practical ways that financial institutions can protect themselves against them.Find out more.
🏢 Funding By Company
Malwarebytes, an endpoint detection and response (EDR) platform, raised a $100.0M Private Equity Round from Vector Capital. (more)
Deep Instinct, a company doing deep learning to protect against zero-day attacks, raised a $62.0M Venture Round from BlackRockandChrysalis Investments. (more)
DataGuard, a continuous compliance and security platform, raised a $60.0M Series B from Morgan Stanley Expansion Capital. (more)
Sardine, a fraud and financial crime prevention infrastructure company, raised a $51.5M Series B from Andreessen Horowitz. (more)
Immunefi, a Web3 bug bounty platform, raised a $24.0M Series A from Framework Ventures. (more)
SecurityPal, a security questionnaire review and automation platform, raised a $21.0M Series A from Craft Ventures. (more)
Hyperlane (formerly Abacus Network), a platform focused on interchain security for distributed ledger technology (DLT) applications, raised a $18.5M Seed from Variant. (more)
Codacy, a code quality and security platform, raised a $15.0M Series B from Bright Pixel. (more)
LayerX Security, a remote browser isolation platform, raised a $8.0M Seed from Glilot Capital Partners.
Operant Networks, a secure networking platform for accessing SCADA systems, raised a $3.8M Seed from Constellation Technology Ventures. (more)
Armorblox, an email security platform, raised an undisclosed Venture Round from S Ventures. (more)
Interos, a risk management and supply chain monitoring platform, raised an undisclosed Series C from Spark Growth Ventures.
Redinent, an IoT security platform for CCTV cameras and networks, raised an undisclosed Seed from Startup India Seed Fund Scheme. (more)
Salt Security, an API protection platform, raised an undisclosed Venture Round from CrowdStrike Falcon Fund. (more)
Vanta, a continuous compliance and security platform, raised an undisclosed Venture Round from CrowdStrike Falcon Fund. (more)
🤝 Mergers & Acquisitions
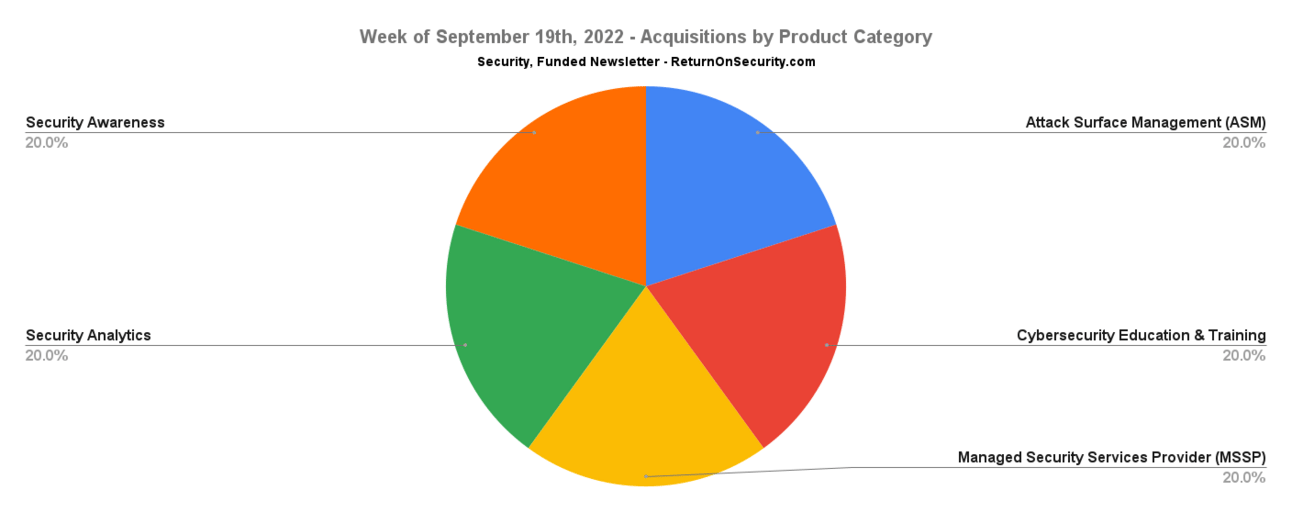
KnowBe4, a security awareness and simulated phishing training platform, received a go private offer fromVista Equity Partnersfor $4.2B. (more)
Cosant Cyber Security, a cybersecurity training and education company, was acquired by GMI for an undisclosed amount. (more)
Reposify, an external attack surface management platform, was acquired by CrowdStrike for an undisclosed amount. (more)
🔐 Secure The Job
If you're looking for new opportunities (actively or passively), I've got two ways to help:
Return on Security Job Board - Browse the jobs I curate each week and apply for what matches your interests.
Return on Security Talent Collective - If you're open to hearing about new opportunities, apply to my talent collective to get personally matched with high-growth, high-upside opportunities. You can join publicly or anonymously, and leave anytime. And it's completely free for candidates.
Are you hiring? Post a role or request access to start meeting world class candidates open to new opportunities. Learn more or request access here.
📚 Great Reads
Kubernetes Security For CISOs - The top five security measures that CISOs should be thinking about for any Kubernetes implementation.
The Cyber Resilience Act - European Commission proposes the Cyber Resilience Act to mandate the secure development of software, including creating SBOMs and having vulnerability handling during the product lifetime.
On Trust and Transparency in Detection - Security teams are beginning to place much greater emphasis on being able to understand how a detection machine made a decision.
You can see the full list of curated posts across all issues here, and you can submit an article, post, tweet, or video here and it can show up in the newsletter!
🧪 Labs
Cybersecurity in a nut shell. pic.twitter.com/DwmjWkvZHq— Alex/Muldwych 💻 (@Muldwych) September 11, 2022
👋 Thanks
Have questions, comments, or feedback about this issue? I'd love to hear from you. Reach out on Twitter or reply directly to the newsletter version of this issue.
Thanks for reading and see you again next time!
Whenever you're ready, there are a few ways I can help you:
Cheers,
Mike P