Hey there,
I hope you had a great weekend!
In this week's issue:
Setting a new precedent
Tech spending is still going up
Debt rules everything around me (D.R.E.A.M.)
It was a sobering week for many in the cybersecurity community last week.
News that Joe Sullivan, Uber's first CISO, was convicted for his role in a 2016 breach that the FTC said he covered up. He may be sentenced for up to eight years in prison as a result. This conviction is both precedent setting and demoralizing for the entire cybersecurity industry.
The threat landscape has changed exponentially since this breach in 2016. Fueled largely by the business of ransomware from organized crime gangs, the productization of the cyber risk insurance market (with hefty funding rounds and valuations), and over-correcting regulations attempting to "brute force" the problem away, the sins Joe Sullivan were convicted of have somewhat become commonplace in today's world.
I was on a podcast this past week where I talked about this topic and how it has created a flywheel that stands to benefit security practitioners the least. More facts and information will continue to be uncovered as time goes on, but as for my initial reaction knowing what I know now - this is bad for the future of our industry.
In funding related news - debt financing rounds are the new gold.
No cybersecurity companies have gone IPO in 2022 just, but that's not stopping the heavyweights like Arctic Wolf from taking on huge rounds (see below). With public valuations dropping, capital being more scrutinized, and fewer deals happening in the broader markets, taking debt loans to continue growth and acquisitions has become more commonplace than last year.
It's a great bet for everyone involved if the companies can continue their upward growth trends. The key question remains, however - will inflation and slowing economic growth overall tamper this rocketship? 🚀
It's now a matter of playing the waiting game, and the cards are (currently) stacked in favor of cybersecurity companies.
Let's dive in.
Subscribe to Security, Funded
Know what and who is moving the cybersecurity.
📊 Market News
💰 Funding Summary
21 companies raised $1.2B across 18 unique product categories
6 companies were acquired or had a merger event across 4 unique product categories
🧩 Funding by Product Category
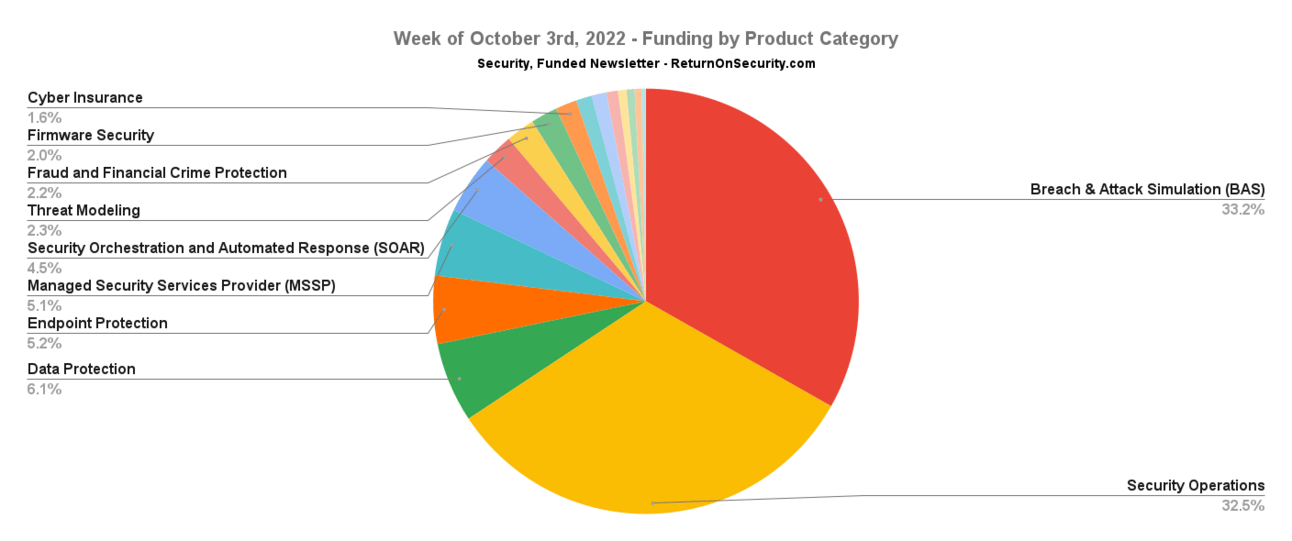
$410.0M for Breach & Attack Simulation (BAS)
$401.0M for Security Operations
$75.0M for Data Protection
$63.9M for Endpoint Protection
$63.2M for Managed Security Services Provider (MSSP)
$55.0M for Security Orchestration and Automated Response (SOAR)
$28.7M for Threat Modeling
$27.0M for Fraud and Financial Crime Protection
$25.0M for Firmware Security
$20.0M for Cyber Insurance
$15.0M for Identity Threat Detection and Response (ITDR)
$13.7M for Threat Intelligence
$10.9M for Professional Services
$8.0M for Secure Networking
$7.5M for Remote Browser Isolation
$6.5M for Application Security
$4.0M for Threat Informed Defense (TID)
$200.0K for Attack Surface Management (ASM)
🗣️ SPONSOR
🗣️Featured Free Event: Fwd: Thinking. The Intelligent Security Summit (powered by Tessian)
CISOs and industry experts are coming together on October 27th to discuss strategies for navigating an ever-changing threatscape, their secrets to building a strong security culture, and how to stop advanced email threats and demonstrate ROI at your organizations.
Access the latest security insights from world-class speakers in just 2 hours.
🏢 Funding By Company
Artic Wolf, a managed cloud security operations company, raised a $401.0M Convertible Note from Owl Rock Capital. (more)
Securiti, a multi-cloud data protection and privacy company, raised a $75.0M Series C from Owl Rock Capital. (more)
ThreatLocker, a platform that adds zero trust policy enforcement to the endpoint, raised a $63.9M Venture Round.
Tines, a security orchestration and automated response (SOAR) platform, raised a $55.0M Series B from Felicis Ventures. (more)
Expel, a SOC-as-a-Service company, raised a $31.0M Series E from CapitalGandPaladin Capital Group.
RealDefense, a managed security services provider (MSSP), raised a $30.0M Debt Financing from Sunflower Bank. (more)
IriusRisk, a threat modeling platform, raised a $28.7M Series B from Paladin Capital Group.
Clearspeed, a platform using voice analytics to assess fraud risk, raised a $27.0M Series C from an individual investor. (more)
Eclypsium, a firmware and hardware security platform, raised a $25.0M Series B from TenEleven Ventures. (more)
Elpha Secure, a cyber risk insurance company, raised a $20.0M Series A from Canapi Ventures. (more)
CrowdSec, an open-source security automation engine with an IP reputation database, raised a $13.7M Series A from Supernova Invest. (more)
Oort, a detection and response platform focused on identity-based threats, raised a $11.5M Series A from .406 VenturesandEnergy Impact Partners. (more)
Narf Industries, a professional cybersecurity services firm focused on research projects and incident response, raised a $10.9M post-IPO equity Round.
Qunnect, a secure quantum network communications company, raised an $8.0M Series A from Airbus Ventures.
LayerX Security, a remote browser isolation platform, raised a $7.5M Seed from Glilot Capital Partners. (more)
Crash Override, an application security platform, raised a $6.5M Seed from Bessemer Venture Partners and SYN Ventures. (more)
Tidal Cyber, a threat-informed defense (TID) platform, raised a $4.0M Seed from Ultratech Capital Partners. (more)
Oort, a detection and response platform focused on identity-based threats, raised a $3.5M Seed from Bain Capital Ventures, Dreamit Ventures, 645 Ventures, and First Star Ventures.
Adarma, a managed security services provider (MSSP), raised a $2.2M Grant from Scottish Enterprise. (more)
Saporo, an attack surface management (ASM) platform, raised a $200.0K Debt Financing from Foundation for Technological Innovation (FIT). (more)
🤝 Mergers & Acquisitions

Blue Hexagon, a cloud detection and response platform, was acquired by Qualys for an undisclosed amount. (more)
Iron Vine Security, a professional services firm focused on cybersecurity services, was acquired by ECS Federal for an undisclosed amount. (more)
Kapstone Technologies, a managed security services provider (MSSP) focused on identity and access management (IAM), was acquired by iC Consult for an undisclosed amount. (more)
StarLink, a managed security services provider (MSSP), merged with Infinigate for an undisclosed amount. (more)
🔐 Secure The Job
If you're looking for new opportunities (actively or passively), I've got two ways to help:
Return on Security Job Board - Browse the jobs I curate each week and apply for what matches your interests.
Return on Security Talent Collective - Apply to my talent collective to get personally matched with high-growth, high-upside opportunities.
Are you hiring? Post a role and request access to start meeting world-class candidates open to new opportunities. Learn more or request access here.
📚 Great Reads
Two CISOs discuss the conviction of ex-Uber CISO - Andrew Monaghan had Ben Halpert, the CISO of Groupon, and myself on the Sales Bluebird podcast to talk about what the sentencing could mean for the cybersecurity industry
Executive Order on Secure Supply Chain — in Plain English - You may have heard about EO 14028, the “Executive Order on Improving the Nation’s Cybersecurity”, which mandates the establishment of minimum supply chain security standards for all software consumed by the US government
What is a software supply chain attack? - Software supply chain security is all the rage these days, and for good reason. A steady increase in attacks over the past decade culminated in the “big one” (so far) in which the Russian SVR penetrated U.S. government networks, a cybersecurity company, and thousands of other targets via the IT company SolarWinds
You can see the full list of curated posts across all issues here, and you can submit an article, post, tweet, or video here, and it can show up in the newsletter!
🧪 Labs
It all starts with a series of tubes. The internet in those tubes eventually evaporates into the environment (WiFi) and if it rises high enough the cooler temperatures cause it to condense into The Cloud
That’s why us-east-1 goes down every time it rains.— a ghost 👻 in some machine (@crayzeigh) November 13, 2020
👋 Thanks
Have questions, comments, or feedback about this issue? I'd love to hear from you. Reach out on Twitter or reply directly to the newsletter version of this issue.
Thanks for reading, and see you again next time!
Whenever you're ready, there are a few ways I can help you:
Cheers,
Mike P